• Data security: OK, you’ve been hacked. How resilient are you?
Yahoo was famously hacked twice, compromising the personal information of one and a half billion of its customers and, ultimately, stunning one of the world’s largest Web companies, undercutting its value and reputation just as it was negotiating a sale to Verizon of its most visible assets.
If recent market studies are any indication, you too have been—or soon will be—the victim of malicious computer software that prevents you from accessing data on your computer unless you pay a ransom for it. The frequency and scope of cyberattacks against manufacturers continues to climb. The FBI suggests ransomware payments will blow through the $1 billion mark this year. In 2015, ransomware payments were estimated at only $24 million.
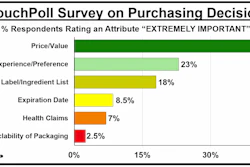
Ransomware attacks “quadrupled in 2016, with an average of 4,000 attacks per day,” notes Limor Kessem, executive security advisor, IBM Security in her report, “Ransomware: How consumers and businesses value their data.” (pwgo.to/2677).
Despite the dramatic rise of ransomware, most CEOs “are dangerously unrealistic about how vulnerable they are,” says cybersecurity consultancy RedSeal, Inc. In fact, based on a recent RedSeal survey of 200 CEOs, “more than 80% display ‘cyber naiveté,’ allowing their global organizations to be exposed to massive cyberattacks.” RedSeal’s research finds that half of the CEOs still prioritize keeping hackers out of their networks, versus just 24% who are concerned with building capabilities to deal with hackers who have successfully breached their network’s perimeter defenses.
If RedSeal’s research conclusions are right, your operations, like those of most manufacturers, are still building walls to keep out intruders who likely have already breached your company’s data perimeters. Instead, argues RedSeal, you should be conducting and continuously upgrading data hacking fire drills to enervate data thieves. “The new cyber battleground is inside the network, not at the perimeter,” says Ray Rothrock, CEO of RedSeal. “Firewalls, virus detectors, and malware scans are required to keep out 99% of the bad guys, but the one percent who get in can cripple a firm, critical infrastructure, or a government agency.”
It’s scary, and not far-fetched, to assume that your packaging operations have been hacked. Focusing on the issue for packaging professionals, the Cybersecurity Group within PMMI’s OpX Leadership Network www.opxleadershipnetwork.org/ is working to “enable safe and secure third-party remote access to improve CPG equipment performance and uptime.”
• Supply chain security: Who’re you dealing with?
“Supply Chain Risk Mitigation in the Pharmaceutical Industry” will be the topic of a Healthcare Packaging & Processing Conference presentation by Chuck Forsaith, Chairman of the Pharmaceutical Cargo Security Coalition (PCSC) and Director, Supply Chain Security of Purdue Pharma LP. The conference is part of PMMI’s PACK EXPO East show in Philly’s Pennsylvania Convention Center, Feb 27-Mar 1 (pwgo.to/2678).
• Product security: “Non BPA Packaging” is part of the appeal
Noticing on Hunt.com that a new pouched tomato paste could be bought in the North Olmsted, OH, Walmart Supercenter, we went searching. Sure enough, there it was: six 1.5-ounce (2 tbsp) laminated foil pouches packed in a lock-bottom, tuck flap paperboard carton, sitting on the top shelf. The pouches remind us of those we saw in Kenya 32 years ago. In Africa then, the driving force behind the packets was economics—sized for Nairobi consumers who could make no more than one-meal-at-a time purchasing decisions.
In the U.S. today, the six pack’s appeal is its convenience (notched for easy opening, “Recipe Ready™ branding), clean label (“tomato paste, citric acid”), and product security (“NON-BPA PACKAGING”) vs. the six-ounce steel can it’s positioned against.
Ben Miyares, Packaging Sherpa, is a packaging market and technology analyst and is president of The Packaging Management Institute, Inc. He can be reached at [email protected].