The spirit of innovation that led to 802.11 wireless radios, and to cellular phones, is very much in evidence throughout the pages of the Gen 2 specification. Its objective was to bring harmony out of the cacophony of competing and otherwise incompatible standards.
With that in mind, consider the following twelve key qualities that position Gen 2 at RFID's center stage:
1. Superior Tag Population Management
The protocol in a nutshell.
If the Gen 2 development effort had a mission statement, its cornerstone would have been the efficient and accurate management of RFID tag populations. To that end, Gen 2 defines the interactions between readers and tags over a robust air interface with three primary command-driven procedures: Select, Inventory, and Access. Let's take a closer look.
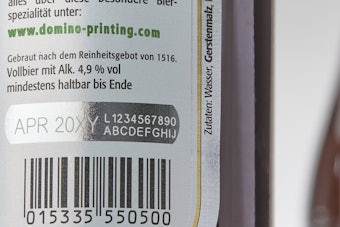
Select–-Prior to conducting an inventory, a user may first wish to conditionally isolate only those tags that exhibit, say, a particular date code, manufacturer code, or other variable of interest. By targeting only that segment of the tag EPC memory that contains those particular kinds of descriptive bits, the reader can quickly narrow down the field, making for a more efficient inventory operation. The Select command offers a quick sorting of the tag population, where the reader (using union, intersection, and negation operators on a set of user-defined selection criteria) chooses a subpopulation of the tags within its field.
Inventory–-The Inventory operation—the real workhorse of the Gen 2 protocol—identifies tags, one at a time, resolves conflicts among tag responses, and sets an appropriate "inventoried" flag within each of the tags as they're counted.
Access–-Available only following an Inventory operation, Access involves more than simply sorting and counting tags. Access commands allow the reader to write individual tag memory fields directly (with EPC and/or password data), set the desired memory lock bits, or kill the tag.
2. Robust Signaling Protocol
A vastly more reliable RF link protocol, Gen 2 slays a Gen 1 nemesis, ghost reads.
Consider the way a Gen 2 reader uniquely identifies a single tag within a population. When a reader issues a Query command, the tag must respond within an extremely narrow window—just four-millionths of a second wide. If the tag does not respond within that timeframe, the reader assumes that no tag is present, and issues another Query command. The reader continues to poll in this manner until it receives a valid response.
This tight window represents the first hurdle in a series of "communication qualifiers" designed to eliminate false triggering on noise and other spurious emissions. When a tag does respond, it does so with a preamble—-a distinctive waveform that the reader is able to reliably discern and identify, even in noisy environments. If the reader does not recognize the preamble as the leading part of the tag's response, it is ignored.
As data begins to flow from tag to reader in the form of well-defined symbols, memory retained in the waveform is used to identify bad sequences, or alternatively, to make decisions on ambiguous bits and fix them. For example, if you were to hear the phrase, “a stitch in time saves pine,” you would know that, based on the history of that set of words, that it should read, “a stitch in time saves nine.” In the same way, through the signaling scheme described in Gen 2, information contained in sequential symbols allows the reader to correct errors as it goes along.
Once the transmission is complete, the reader reviews the waveform and checks the PC (Protocol Control) bits at the top of the transmission, used to compare the number of bits it received with the number of bits the tag says it sent. If the two numbers match, then the reader can be fairly confident of a valid transmission.
But not so fast. The reader then compares the cyclic redundancy check (CRC) at the end of the transmission and verifies its integrity. Only then is the reader satisfied that it has read a valid EPC.
True Gen 2 readers, implementing these checks properly, will have an extremely low probability of seeing ghost reads. In fact, with a properly implemented Gen 2 system, end users should simply not expect or tolerate ghost reads.
3. Dense-Reader Operation
Can you hear me now?
Any truly practical vision of RFID deployment will require the fielding of many readers, all of which might be operating simultaneously, blasting away at full volume, and in fairly close proximity to one another. Faint-voiced tags will have little, if any, hope of being heard above such a din; the noise and interference resulting from of all that shouting will surely bury them. Unless they're Gen 2 tags.
Gen 2 gets around the problem of "dense" readers by isolating tags and readers through a frequency channelization scheme, best illustrated by analogy:
Think of the UHF spectrum as a highway, where readers are semi-trailer trucks, and tags are bicycles. Dense-reader spectral planning effectively divides the UHF frequency band—the highway—into multiple lanes. Trucks are allowed to use certain lanes, while bicycles are permitted to use other lanes. In any case, trucks and bicycles do not share lanes.
Furthermore, trucks are required to remain within the boundaries of their respective lanes, as sideswiping or drifting into the bicycle lanes would prove disastrous (particularly for the bicycles!). In a similar manner, if a reader’s signal (which is many orders of magnitude greater than that of the tags) were to leak into adjacent tag lanes, it would mask the tags' low-power transmissions, burying them in RF noise, and preventing other readers from seeing them at all. By restricting reader transmissions to occur within strictly delineated lanes (or channels), tags can be heard clearly, even though as many as 50 active readers might be operating simultaneously in 50 available channels.
The fact is there is a limited amount of spectrum allocated for UHF RFID (this is particularly true in Europe). A Gen 2 system incorporating only dense-reader capable readers is best able to exploit that space efficiently, and to great effect.
4. Cover-Coding of the Forward Link
Masking information transmitted from the reader to the tag prevents unwelcome snooping.
Maintaining a secure link between reader and tag is essential to safeguard data transmitted over an air interface. It's especially critical in the reader-to-tag direction, because reader transmissions occur at substantially higher power levels than those of the tags, who effectively whisper their responses back to readers. Here's how Gen 2 goes about the enciphering:
The reader requests a random number from the tag. The reader then mixes that random number with its data before transmitting the result to the tag. The tag decodes the mixing (reversing the operation) and extracts the original information. A simple scheme, but it effectively protects both data and password transactions by obscuring data transmissions in a purely random manner.
5. A 32-bit Kill Password
Unauthorized kills are dead in the water.
Incorporated to address privacy concerns, the kill command permanently disables a tag from talking back to a reader, rendering it useless. The ability to kill a tag, though, exposes the network to the possibility of unauthorized kills. To thwart such mischief, a password protection scheme was adopted. In earlier UHF RFID versions, though, it didn't amount to much. Class 1's 8-bit kill password, for example, left it exposed to only 256 possibilities—hardly a password at all. While Class 0 improved things significantly with a 24-bit password, Gen 2 raised the hacker's bar to 32 bits—one of more than 4ꯠꯠꯠ possibilities for a hacker to decode.
6. Sessions Dramatically Boost Productivity
RFID tag to multiple readers: "Take a number."
Capitalizing on the enabling power of the dense-reader mode, Gen 2 also introduces the concept of sessions, where as many as four different readers may access the same population of tags through a time-interleaved process. That's an extremely useful capability. Consider when a shelf-mounted reader in the midst of a counting operation (assigned to, say, session 1), is interrupted by another reader entering the field—possibly a handheld reader—to perform its own inventory operation (in session 2, perhaps). Dock door and forklift readers, assigned to sessions 3 and 4 respectively, might also jump in for a round. Because Gen 2 tags maintain a separate "inventoried" flag to keep track of each of these various random and independent sessions, they're able to seamlessly resume their participation in the previous (pre-interruption) inventory round, picking up right where they left off, and never miss a beat.
7. Significantly Faster Singulation Rates
Tag, you're it.
Readers and their associated tag populations have a lot of business to transact. At least one throughput-gating parameter is the effective data rate, which also determines the time it takes to singulate, or identify, a single tag within a population. Typical Gen 1 data rates run from 55 to 80 kbps. Pretty fast.
Gen 2, though, provides for data rates as high as 640 kbps (a throughput of 1길 tags per second). That's on the order of a ten-fold performance improvement over Gen 1.
8. Variable Read Rates
Faster is better—sometimes.
The rate of data flow between reader and tag is governed by a number of factors: environmental conditions (including noise level and physical structures), region of operation, the number of active readers in the area, and even the speed of tagged materials moving through the distribution center. A very adaptable system, Gen 2 allows the fine-tuning of the RFID network—including the varying of data rates—to optimize performance across all possible combinations of operating conditions. Whether the need is for fast reads of pallets moving through a dock door, or slower reads in a noisy environment of dense readers, Gen 2 is able to flex.
9. Greater Configuration Control
Flexible communication formats allow the tailoring of the Gen 2 system to its specific operating environment.
The modulation and data encoding schemes of choice, like the selection of data rates, also depend on a set of environmental considerations. As such, Gen 2 provides options in both reader-to-tag link and tag-to-reader link directions, allowing performance calibration of the Gen 2 system to the demands of its operating environment. Gen 1 systems, on the other hand, are limited to a fixed communications format, where one size may not necessarily fit all.
10. Worldwide Operation
Gen 2 RFID plays on the world stage.
Both Gen 1 and Gen 2 systems cover the 860 to 960 MHz operational band—the superset of international frequencies—but the way the two standards deal with that spectrum is worlds apart. As far as Europe is concerned, Gen 1 doesn't deal with it very well. Compared with North America's fairly wide frequency allocation of 902 to 928 MHz, Europe's is pretty slim—just 865 to 868 MHz. As such, European RFID deployments tolerate much less interference, and require much tighter spectral control than Gen 1 systems can deliver. Gen 2, on the other hand, takes the European standards fully into account; it works well in North America, Japan, Europe, and elsewhere, making Gen 2 a truly international standard, hence its strong advocacy within ISO.
11. Improved Manufacturability
Better, faster, smaller, cheaper.
Gen 2 tag chip design lends itself well to very large scale integration. The new standard exhibits a greater emphasis on digital logic; as Moore’s law continues to shrink fabrication geometries, Gen 2 chips will get ever smaller still.
12. The 12th Man
The whole is greater than the sum of the parts.
While each of the foregoing features represents a significant performance improvement over Gen 1 offerings, when taken together, they leverage much more. Further, as Gen 2 systems are field tested, it will become apparent that perhaps the greatest lever of all is the communications systems engineering expertise behind the specific implementations. This is where the Gen 2 standard will be forged into proven elements that comprise a working system solution.
This article was authored by Impinj’s Chris Diorio, cofounder chairman, and John Schroeter, writer.